Wireguard Gateway & Android
Setup your Linux Server
Your Linux server should be accessible via a public IP by UDP. If the IP address changes, use DynDNS.
First install WireGuard on your Linux server. On the official website you will find the right way for your Linux distro: WireGuard.com/install
Then configure the Gateway. We will use the range 100.64.0.0/10 (RFC 6598) because it doesn’t colide with private IPv4 adresses (RFC 1918).
echo '[Interface]' > /etc/wireguard/wg0.conf
echo "PrivateKey = $(wg genkey)" >> /etc/wireguard/wg0.conf
echo 'ListenPort = 50002' >> /etc/wireguard/wg0.conf
echo "Address = 100.64.0.1/10" >> /etc/wireguard/wg0.conf
iptables -t nat -A POSTROUTING -s 100.64.0.0/10 -o eth0 -j MASQUERADE
systemctl enable --now wg-quick@wg0
Don’t forget to save the iptables rules for the next start. The easiest way is to include this config in wg0.conf: PostUp = iptables -I FORWARD -i eth0 -j ACCEPT; iptables -I FORWARD -o eth0 -j ACCEPT; iptables -t nat -I POSTROUTING -o eth0 -j MASQUERADE PostDown = iptables -D FORWARD -i eth0 -j ACCEPT; iptables -D FORWARD -o eth0 -j ACCEPT; iptables -t nat -D POSTROUTING -o eth0 -j MASQUERADE
To get the public key (you need it later on):
wg pubkey <<<$(grep PrivateKey /etc/wireguard/wg0.conf | cut -d ' ' -f3)
Now the gateway is configured and running. To get some information, type in wg and use systemd:
systemctl status wg-quick@wg0
wg
Enable IP forwarding in the Linux kernel by uncommenting or adding (uncommenting) net.ipv4.ip_forward = 1 in /etc/sysctl.conf to persist the setting between system restarts. Use sysctl -w net.ipv4.ip_forward=1 to enable IP forwarding immediately without having to reboot.
Setup your Android
Download the App from F-Droid or Google Play.
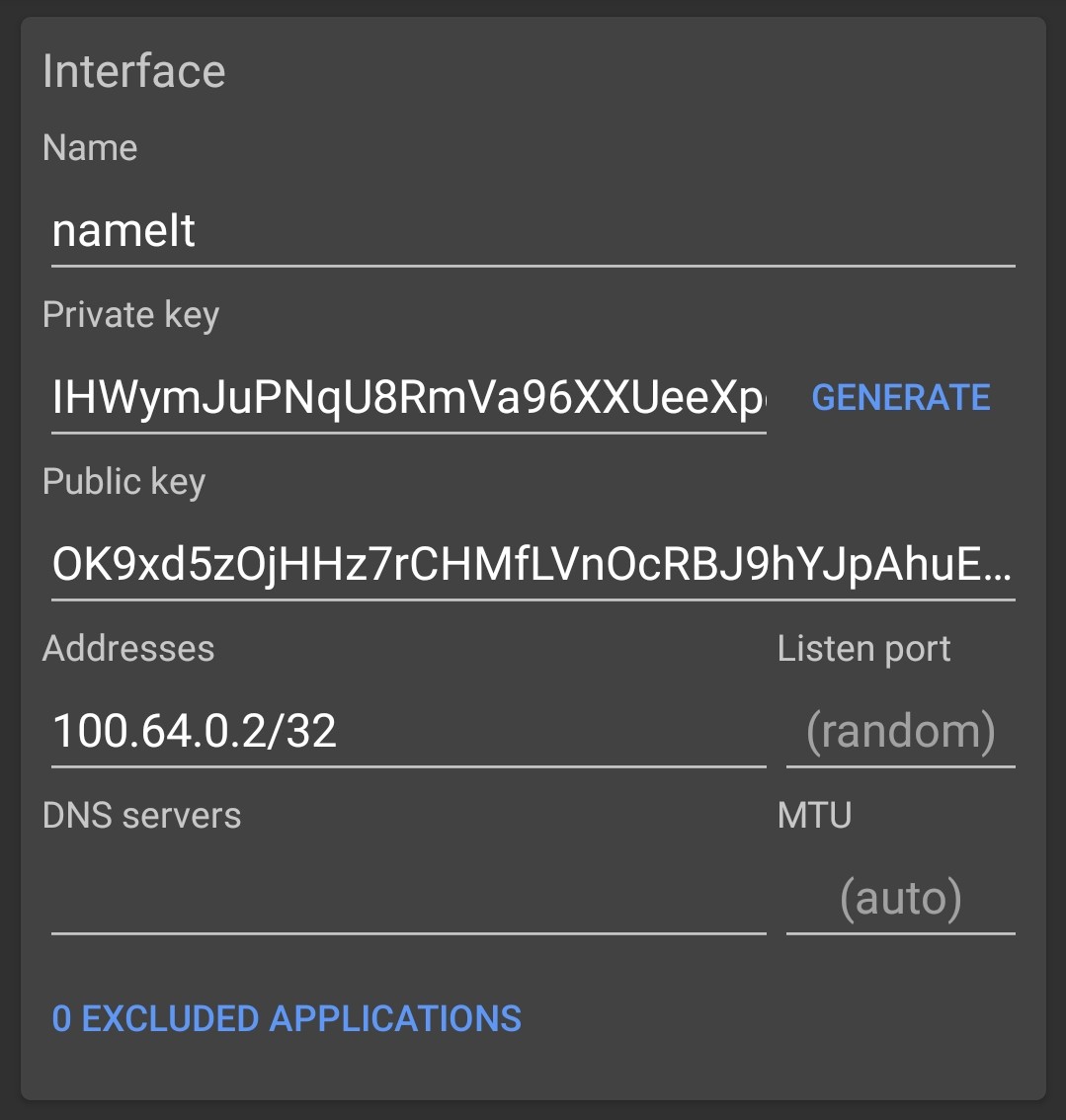
In WireGuard, you must manually set an IP address for each client. The 100.64.0.0/10 area has hosts from 100.64.0.1 to 100.127.255.254, the first one is already occupied by the gateway, so we use 100.64.0.0.2.
 |
 |
 |
|---|---|---|
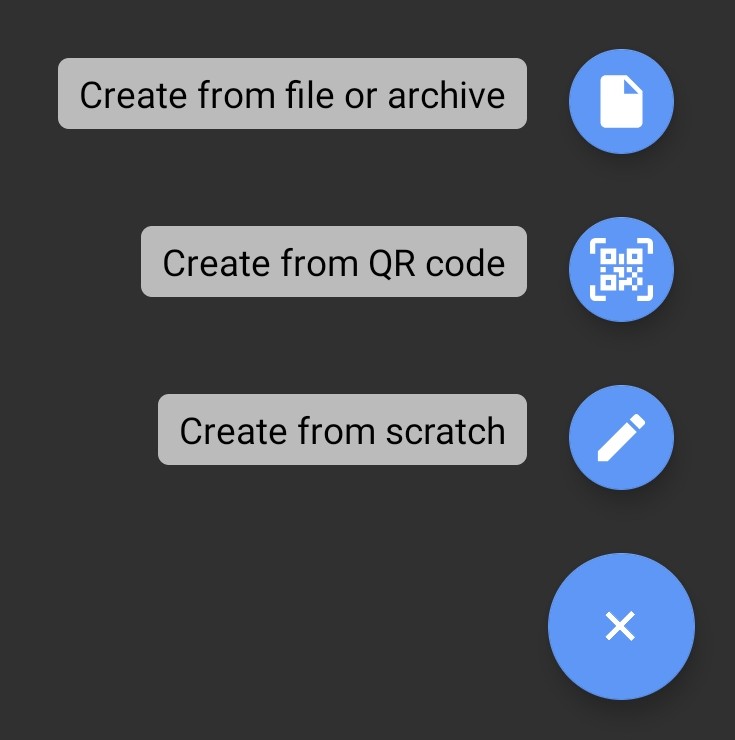
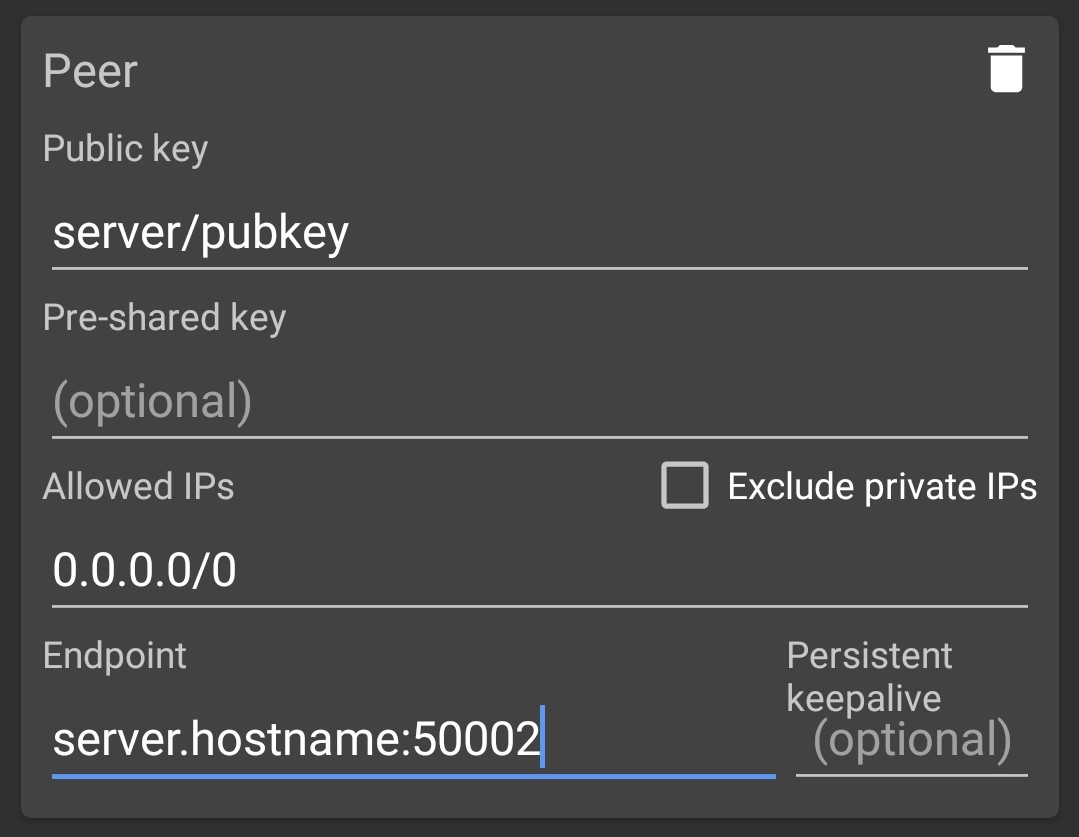
| Open the app and “Create from scratch” | Generate a key pair. Make a note of the public key, you will need it later. Name the configuration and add the client IP address with 32 mask. | Add a peer. Now enter the gateway information. Allowed IPs is 0.0.0.0/0. |
Add Android Client to Server
Now add the client information to the gateway and restart the interface.
[Peer] >> /etc/wireguard/wg0.conf
PublicKey = <Client-Pub-Key> >> /etc/wireguard/wg0.conf
AllowedIPs = 100.64.0.2/32 >> /etc/wireguard/wg0.conf
systemctl restart wg-quick@wg0 && systemctl status wg-quick@wg0
Sources
Heise Besser tunneln
Witepaper WireGuard: Next Generation Kernel Network Tunnel
Demo Video Test WireGuard VPN net roaming